How Changing DNS Can Improve the Security of Our Network
One of the main pillars of cybersecurity is the DNS. The Domain Name System is an intangible element of the Internet. Every time we research something on the Internet, the DNS gets activated by displaying in our browser the website we are looking for.
People use DNS thousands of times a day without even knowing it: every time a user connects to a website, opens an app on their phone, or updates software, their device queries DNS servers to find the IP address associated with the domain.
Most organizations don’t bother to secure the DNS layer, but they should, and even home users should be able to make modifications in their network to secure DNS.
LEARN HOW TO ADD AN EXTRA LAYER OF SECURITY BY REPLACING THE DNS SERVERS IN YOUR BROWSER
In simple words dns works like a phone book: if you want to call someone you check the phone book to get their phone number; similarly, if you want to open a website, the dns gives you the IP address for that website.
To open a website, you need to know its server IP address because computers only understand IP addresses and not domain names, but can you imagine if we were all forced to remember each IP address for every website we visit? That is impossible and that’s why DNS kicks in.
We just have to remember the domain name and the dns will resolve the IP address for that domain.
POTENTIAL ISSUES IF YOU OR YOUR IT DEPARTMENT DOESN’T SECURE YOUR DNS
The problem of not securing the dns is due to an old misconception that it would be enough to install an antivirus on your pc or MAC and your computer will be enough protected. The second error is based on the conviction that the DNS servers installed in the routers of the major ISP such as the ones operating in Westchester, NY, Connecticut (Optimum and Verizon) are safe enough and we should not be bothered changing the DNS in our routers.
As a matter of fact, there are DNS attacks that can be carried forward and that can redirect our Internet searches in places where we don’t want to be and where criminals live and prosper. Here are some of these DNS attacks:
1- DNS Hijacking: it occurs when cyber criminals hack the dns either by changing the dns server address or by intercepting the communication between your device and the dns server. After hacking, perpetrators replace the actual server IP address with their site. For example, if you try to open google.com you will be redirected to the hackers’ page where fake advertisements or bogus websites will try to steal your confidential information.
2- DNS Spoofing and DNS Cache Poisoning: dns spoofing is an attack in which the attackers spoof the dns result without changing the dns server settings on the end user computer: a typical dns spoofing act is cache poisoning or dns poisoning. In dns cache poisoning the attacker spoofed the dns cache by redirecting the user to the malicious site. The dns cache is used to speed up the dns resolve process when you open a website its IP address is resolved from the dns server then it is stored as a dns cache so that you don’t have to contact the dns server again next time you try to open the same website the dns cache stored on your computer quickly resolves the IP address speeding up the whole process. Hackers can poison this cache by replacing the IP address, so you are directed to their malicious site instead of the actual site.
The difference between dns spoofing and dns hijacking is that dns hijacking or (aka dns redirection) typically involves malware infection that changes the dns settings on user’s computer. Malware replaces the dns server address with the malicious one so all dns queries are sent to the hacker’s dns server. DNS spoofing, on the other hand, is an act where hackers spoof the dns records cached on your computer and use it to their own advantage.
HOW YOU CAN PROTERCT YOUR NETWORK FROM DNS HACKING
1- Install a good antimalware product such as Malware bytes. The reason why I recommend Malware bytes is because it has a free browser security plugin, Malware Browser Guard, which will shield up all the Internet searches you make and block all the nasty popups that can lead to hijacking your DNS.
2- Use DNS Security: if you own or run a website, you should enable this feature that will enhance the security of the DNS by using cryptographic keys. Basically, DNSSEC creates a chain of trust through encrypted keys that cannot be spoofed or intercepted by criminals.
3- Change the Default Password of your Router: as I have reiterated many times, I recommend to avoid the username admin anywhere in our network but if you cannot change the word admin, try to create a very complex password made of multiple types of characters (minimum 10).
4- Use a VPN: vpn allows you to browse the internet securely and the chances to get hijacked are reduced to a minimum, because VPN creates a safe tunnel between your searches and the VPN provider.
5- Use Secure DNS: if you are able to replace the DNS servers in your router with safe DNS servers such as Google public DNS, Cloudflare or Cisco Open DNS, all the queries your network will make will be resolved to your browser after a check of trust is made by these much safer DNS servers.
Here is the list of the main free Public DNS providers:
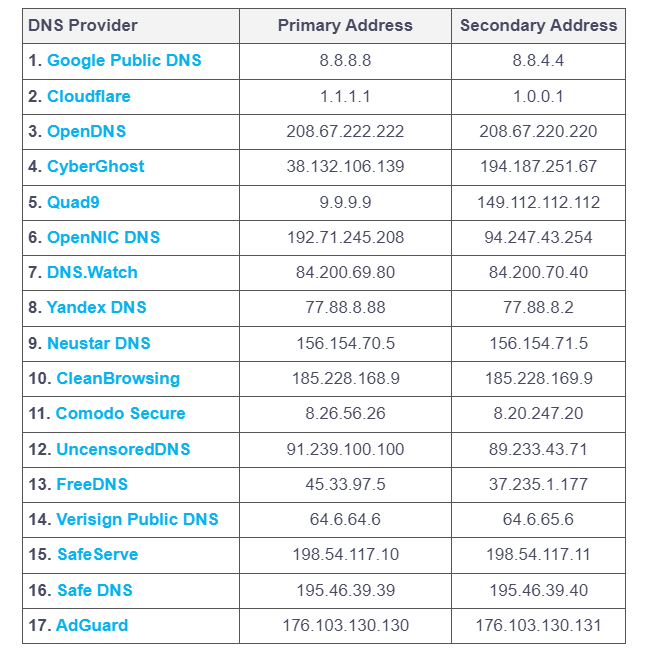
I would just go with Google, Cloudflare or Open DNS and would live the others as a backup. The table above shows Primary Address and Secondary Address because the DNS have to be redundant, that is, if the primary is unavailable, the secondary will step in and viceversa.
WHAT PUBLIC DNS DON’T DO TO YOUR NETWORK
1- DNS do not replace your antivirus: DNS should be used in addition to the antivirus software you use. the task of replacing the DNS in your router should be one of the several ways in which you can secure your network and not the only way.
2- DNS will not make your Internet faster: DNS will make your internet more secure but not faster. To make your Internet faster, check first your cable bill and make sure that you have matched the speed of your Internet with what you are paying for. If you are already paying for higher speeds and are not getting them, call the cable company and ask them to match the speed package with the real speed. If you need faster Internet, you may call your ISP, which in Westchester county are Optimum, Verizon, Spectrum.
3- DNS does not secure your email: Let me clear about this point: DNS does not secure the email you use because emails are secured with a different process that involves the MX records. On the other hand, if you check your email with your browser, having secure DNS and Malware Bytes Browser plugin installed, will defintely grant you a safe acces to your web browser email.